Recent Articles
Quickest Mobile Data Recovery Case: 100% of Data Recovered in One Hour
How to fix a corrupted database on PS4
How to Troubleshoot Black or Blank Screens in Windows
LockBit Ransomware: A Comprehensive Guide to the Most Prolific Cyber Threat
How To Use iPad Recovery Mode
How to Prevent Overwriting Files: Best Practices
External Hard Drive Not Showing Up On Windows – Solved
How to Fix a Corrupted iPhone Backup
Backup and Remote Wiping Procedures
Common VMware Issues and Troubleshooting Solutions

I think there's an issue with my storage device, but I'm not sure Start a free evaluation →
I need help getting my data back right now Call now (800) 972-3282
BianLian is a malware infection, active since early 2022, that encrypts the data and locks the files until a ransom is paid (ransomware). However, lately, the BianLian hacker group changed their tactics to extortion, as Avast released a decryptor for BianLian ransomware. This tactic is known as double extortion.
BianLian ransomware developers target enterprises in several industries, such as banks, manufacturers, insurance companies, education, healthcare, and more.
They target most English-speaking countries and have not claimed any affiliation with any nation-state or agenda. Actually, they seem to be financially motivated rather than having political motivations.
After encrypting the data, it renames the files adding the .bianlian file extension to them and drops a ransom note named “Look at this instruction.txt” at the desktop.
What kind of malware is BianLian?
BianLian is ransomware, a type of malware that encrypts and locks the victims’ files and then requests a ransom in exchange for the decryption key. It is cross-platform ransomware that encrypts the victim’s files and they also work with the double extortion tactic, threatening to leak the data into the dark web if the ransom is not paid.
As a cross-platform ransomware, BianLian can access and operate in different operating systems and environments
Everything we know about BianLian ransomware
Confirmed Name
- BianLian virus
Threat Type
- Ransomware
- Crypto Virus
- Files locker
Encrypted Files Extension
- .bianlian
Ransom Demanding Message
- Look at this instruction.txt
Is There a Free Decryptor Available?
- Yes, there’s a decryption key for BianLian by Avast
Does the decryptor work?
Yes, Avast free BianLian decryptor work to unlock encrypted files. The threat actors changed their tacts to double extortion since the decryption key is effective.
Detection Names
- Avast Win32:Dh-A [Heur]
- Emsisoft Trojan.GenericKD.61254969 (B)
- Kaspersky Trojan-PSW.Win32.Stealer.aosa
- Malwarebytes Ransom.Bianlian
- Microsoft Ransom:Win64/Bianlian!MSR
- Sophos Mal/Generic-S
Symptoms
- Cannot open files stored on your computer
- New file extensions
- A ransom demand message on your desktop
- Files renamed with random letters
Distribution methods
- Infected email attachments (phishing emails)
- Torrent websites (infected links or files)
- Malicious ads (malvertising)
Consequences
- Locked files
- Stolen passwords
- Data breach
Prevention
- Antivirus and anti-malware
- Updated software
- Updated operating system (OS)
- Firewalls
- Don’t open an email attachment from an unknown source
- Do not download files from suspicious websites
- Don’t click on ads unless you’re sure it’s safe
- Only access websites from trustworthy sources
How did BianLian infect your computer
BianLian ransomware’s primary infection method is via ProxyShell vulnerabilities. Once in, BianLian uses the living off the land (LoL) techniques for network profiling and lateral movement.

BianLian encryption and ransom note
BianLian developers built the ransomware using the Go programming language (aka Golang).
It adds a ransom note to the desktop where the cybercriminals threaten to leak the data unless the ransom is paid.
Example of the ransom note:
Your network systems were attacked and encrypted. Contact us in order to restore your data. Don’t make any changes in your file structure: touch no files, don’t try to recover by yourself, that may lead to it’s complete loss.
To contact us you have to download “tox” messenger: hxxps://qtox.github.io/
Add user with the following ID to get your instructions:
A4B3B0845DA242A64BF17E0DB4278EDF 85855739667D3E2AE8B89D5439015F07E81D12D767FC
Alternative way: swikipedia@onionmail.org
Your ID: –
You should know that we have been downloading data from your network for a significant time before the attack: financial, client, business, post, technical and personal files.
In 10 days – it will be posted at our site hxxp://bianlianlbc5an4kgnay3opdemgcryg2kpfcbgczopmm3dnbz3uaunad.onion with links send to your clients, partners, competitors and news agencies, that will lead to a negative impact on your company: potential financial, business and reputational loses.
How does BianLian ransomware work
BianLian starts servers in Windows Safe Mode and then executes its file-encrypting malware while evading detection by system-installed security solutions. It also deletes snapshots, removes backups, and runs its Golang encryption module via Windows Remote Management (WinRM) and PowerShell scripts.
BianLian is proficient in lateral movement, so it can collect data for double extortion. After encrypting the data and dropping the ransom note, hackers give 10 days for the victims to pay their demands or they leak the data.
Prevent the BianLian ransomware attack
Preventing ransomware attacks is easier and cheaper than recovering from them. We already mentioned several ways you can prevent BianLian ransomware attacks. Here is a complete list of what to do to keep your data and business safe.
1. Use strong passwords
Always use strong and unique passwords for each account and only share them with necessary people. For example, if an employee doesn’t require a website account or software for their work, they don’t need access to it. This can guarantee that only authorized personnel will access each company account.
2. Apply multi-factor authentication
You can use two-factor authentication or biometric unlock to ensure that only authorized people have access to folders, devices, or accounts.
3. Erase outdated and unused user accounts
Unused accounts are vulnerabilities that hackers can exploit. Deactivate and close unused accounts as well as those used by past employees.
4. Keep software updated
As mentioned, outdated software is a weak point. That’s because new updates can create protection against new types of malware, such as BianLian.
5. Schedule regular backups
Keep at least three copies of your data, having at least one stored offline and off-site. This can guarantee that, even if you’re hit by a disaster, being natural or human-made (like ransomware), your data is always safe.
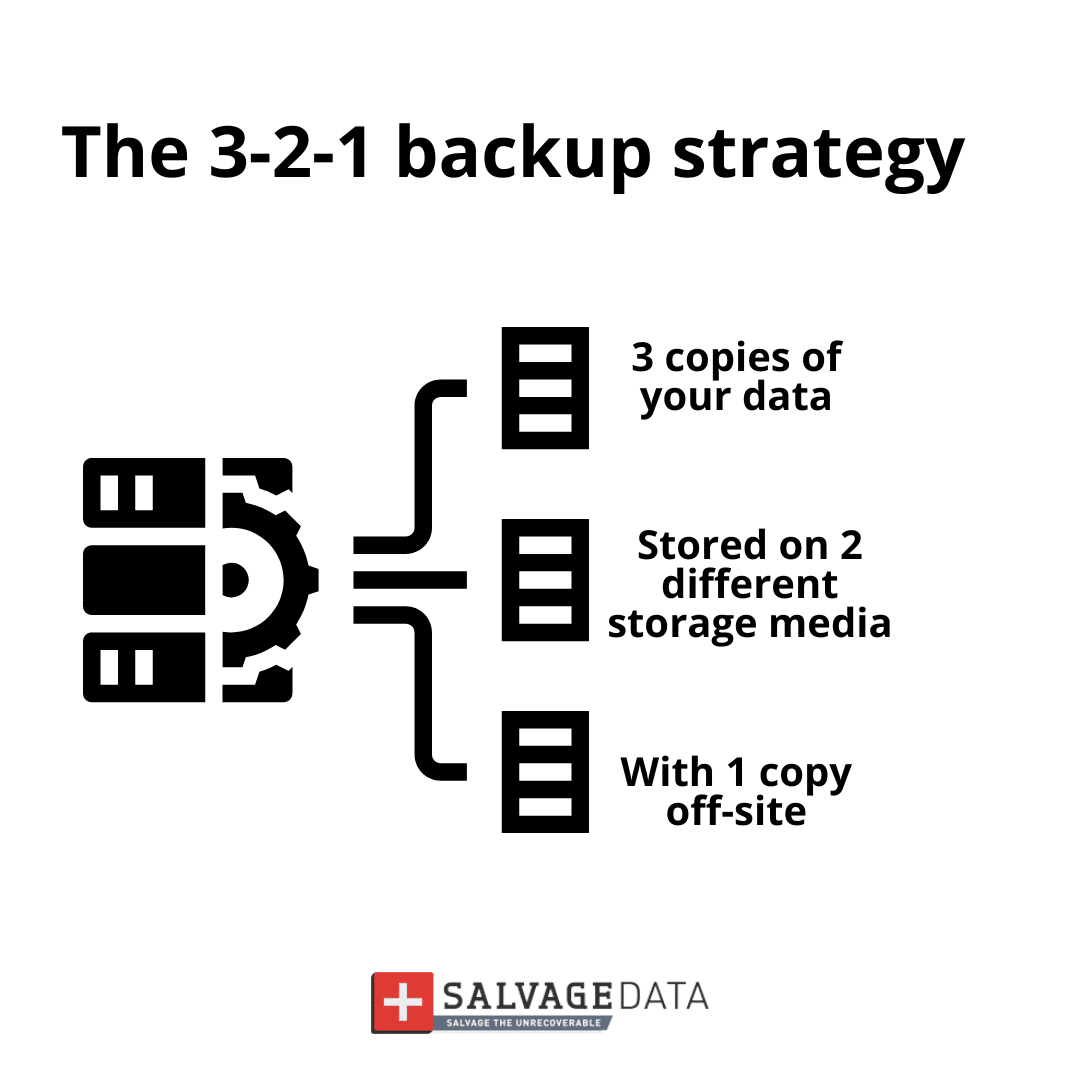
Regular backups can prevent downtimes and ensure you never lose any sensitive data.
6. Use a cybersecurity solution
You can either have an IT team to guarantee your business security or hire a cybersecurity service.
Either way, you must look for vulnerabilities in the network, such as back doors, exploit kits, and youtube software.
7. Have a recovery plan in hand
Data recovery plans are documents that work as guides on what to do in case of a disaster. This can help you restore your business faster and more securely.
See how to create a data recovery plan with our in-depth guide.
How to recover from the BianLian attack
The first step to recover from the BianLian attack is to isolate the infected computer by disconnecting from the internet and removing any connected device. Then, you must contact local authorities. In the case of US residents and businesses, it is the local FBI field office and the Internet Crime Complaint Centre (IC3).
To report a ransomware attack you must gather every information you can about it, including:
- Screenshots of the ransom note
- Communications with BianLian actors (if you have them)
- Sample of an encrypted file
You must not delete the ransomware, and keep every evidence of the attack. That’s important for digital forensics so experts can trace back to the hacker group and identify them. Is using the data on your infected system so that authorities can investigate the attack and find the responsible. A cyber attack investigation is not different from any other criminal investigation: it needs evidence to find the attackers.

After isolating the device and contacting authorities, you must follow the next steps to retrieve your data:
1. Contact your Incident Response Retainer
A Cyber Incident Response is the process of responding to and managing a cybersecurity incident. An Incident Response Retainer is a service agreement with a cybersecurity provider that allows organizations to get external help with cybersecurity incidents. It provides organizations with a structured form of expertise and support through a security partner, enabling them to respond quickly and effectively in the event of a cyber incident.
An incident response retainer offers peace of mind to organizations, offering expert support before and in the aftermath of a cybersecurity incident. The specific nature and structure of an incident response retainer will vary according to the provider and the organization’s requirements. A good incident response retainer should be robust but flexible, providing proven services to enhance an organization’s long-term security posture.
2. Identify the ransomware infection
You can check which ransomware infected your machine by the file extension (some ransomware uses the file extension as their name), or it will be on the ransom note. With this information, you can look for a public decryption key.
Since BianLian has a free decryptor, you can use it to restore your files. Download the free decryptor here.
3. Remove the ransomware and eliminate exploit kits
Before recovering your data, you must guarantee that your device is ransomware-free and that the attackers can’t make a new attack through exploit kits or other vulnerabilities.
However, paying the ransom doesn’t guarantee you will get the key or that it will work. Besides, there’s the risk of financing criminal activities and even terrorism. For these reasons, DO NOT PAY THE RANSOM.
Instead, contact local authorities and work on restoring your data and removing the BianLian ransomware from your computer or business network.
A ransomware removal service can delete the ransomware, create a forensics document for investigation, eliminate vulnerabilities, and recover your data.
4. Use a backup to restore the data
Backups are the most efficient way to recover data. Make sure to keep daily or weekly backups, depending on your data usage.
5. Contact a ransomware recovery service
If you don’t have a backup or need help removing the ransomware and eliminating vulnerabilities, you should contact a ransomware data recovery service.
SalvageData experts can safely restore your files and guarantee that BianLian ransomware does not attack your network again. Contact our experts 24/7 for emergency recovery service or find a recovery center near you.